The United States government will pay you $15 million for information on LockBit ransomware gang

In a bid to apprehend the gang behind the devastating LockBit ransomware site, the United States of America has offered up a bounty worth $15 million to anyone with information
|GETTY IMAGES

LockBit criminals are estimated to have made $120 million from ransom payments
- US officials have offered a $15 million bounty for information on the LockBit gang
- That's twice the amount awarded in the latest National Lottery prize draw
- A Tor SecureDrop server has been set-up to anonymously submit information
- LockBit impacted 200 victims in the UK, including NHS hospitals and Royal Mail
- Law enforcement shut the LockBit website this week
- But experts believe LockBit could soon rebuild its network
Don't Miss
Most Read
The United States government is offering an eye-watering $15 million bounty to anyone who provides new information about the LockBit ransomware gang and its associates.
The life-changing money comes from an initial $10 million for information that could help law enforcement identify or locate the leadership team behind the devastating software, while there’s an extra $5 million up for grabs if you can offer a tip that points to associates of the LockBit gang.
That’s roughly £11.9 million converted ...or roughly twice the £5.4 million prize fund available in this week’s National Lottery draw.
The team behind LockBit have made over $120 million in ransom payments from over 2,000 victims, the US Department of Justice estimates. It's not uncommon for perpetrators to demand over $1 million in a single ransom.
If you submit a useful tip, the reward will be paid by the Transnational Organized Crime Rewards Program (TOCRP). This US government arm has already paid out more than $135 million since 1986. The US State Department has provided a dedicated Tor SecureDrop server that lets you anonymously submit tips on LockBit, its associates, or any other wanted criminals.
The online repository established by LockBit to sell hacking software used in thousands of ransomware attacks worldwide was taken down this month. There were over 200 victims of LockBit alone in the UK, including the Royal Mail and public service bodies like NHS hospitals.
Director General of the National Crime Agency (NCA), Graeme Biggar said: “We have hacked the hackers; taken control of their infrastructure, seized their source code, and obtained keys that will help victims decrypt their systems. As of today, LockBit are locked out. We have damaged the capability and most notably, the credibility of a group that depended on secrecy and anonymity.”
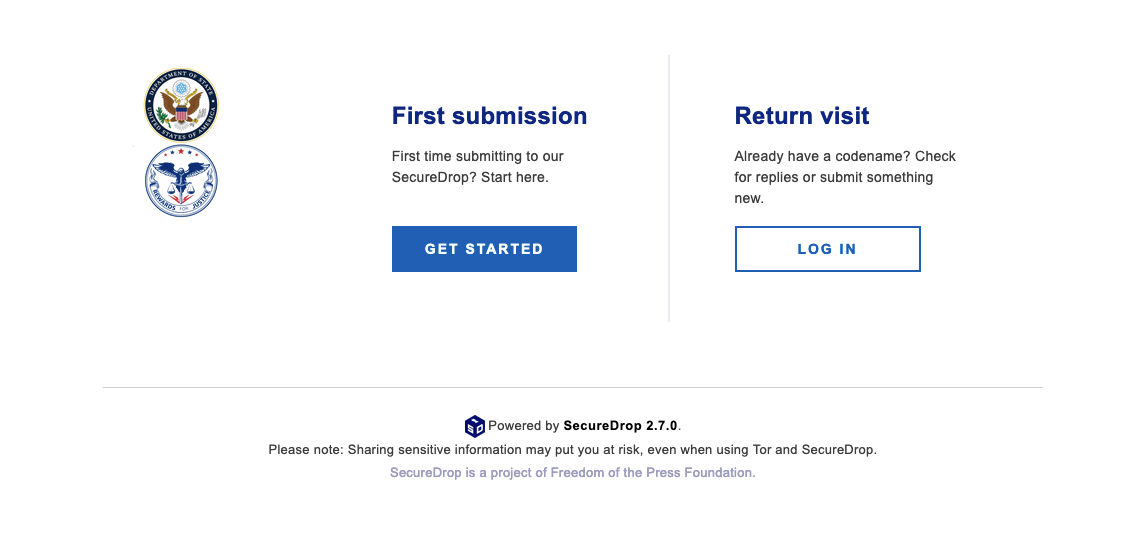
The United States State Department has established a secure file-drop system, only available to those running the anonymous Tor web browser, to submit files or other information linked to the LockBit gang
|UNITED STATES DEPARTMENT OF STATE
The gang behind the software used marketing tactics including paying $1,000 to customers who had the logo tattooed on themselves as well as payouts for anyone who spotted an error in their code. The latter is used by some of the biggest technology companies on the planet, including Google and Microsoft, to improve the quality of their products and swerve attacks from hackers.
US authorities have charged five Russians in relation to LockBit, and two other suspects have been arrested in Poland and Ukraine. Around 200 cryptocurrency accounts have also been frozen by investigators.
The site had been used by LockBit to sell services, including ransomware, to hackers which would allow them to breach people’s computer networks.
As the name suggests, ransomware is a type of malicious code that locks people out of their own systems and files – demanding a ransom payment to get access to their data again.
NCA investigators found that the gang behind the ransomware attacks did not always delete data when victims paid ransoms. It said it has found more than 1,000 decryption keys held by hackers and will be contacting UK-based victims to help them recover encrypted data.
Two of the suspects charged by the US are in custody, Mikhail Vasiliev, who is being held in Canada awaiting extradition, and Ruslan Magomedovich Astamirov, who is in the US.
The remaining three, Artur Sungatov, Ivan Kondratyev and Mikhail Pavlovich Matveev, are at large.
The NCA said the infrastructure supporting LockBit’s tool that was used to steal data, known as StealBit, based in three countries, has also been seized.
Hundreds of people are thought to have been involved in running the group.
Mr Biggar said: “Through our close collaboration, we have hacked the hackers; taken control of their infrastructure, seized their source code and obtained keys that will help victims decrypt their systems.”

Visiting the LockBit website now returns the following image, informing customers about the recent takedown by law enforcement
|REUTERS
Paul Foster, head of the NCA’s national cybercrime unit, said that LockBit’s popularity was partly because it was so easy to use.
He said: “LockBit had established itself as the preeminent ransomware strain over the last four years and one of the reasons for this was its intuitive platform and its relative ease of use. That means just with a few simple clicks even the less technically savvy cybercriminals used LockBit to deploy ransomware.
“Another key reason for their past criminal success was the marketing and branding that underpinned LockBit. They had a slick website and they had loyal customers. They ran a successful marketing campaign that included a promise to pay $1,000 to anybody who had the LockBit logo tattooed on themselves.”
Experts said that while LockBit may rebuild its network, the law enforcement action is a major setback.
Chris Morgan, senior cyber threat intelligence analyst from cybersecurity firm ReliaQuest said: “The operation carried out by law enforcement against Lockbit could potentially be the most significant action taken against ransomware so far.
“The success of the law enforcement operation will be dictated over whether Lockbit are able to recover their operations. ReliaQuest has observed Lockbit as the most active and prolific ransomware groups for several years, who will likely have significant resources and backup infrastructure capable of recovering operations and showing resilience.
“The operation will however likely deal a significant short term blow to the group’s operations, sowing distrust throughout the groups affiliates over potential law enforcement compromise.”
LATEST DEVELOPMENTS
- Your Android phone is likely beaming data to China and Russia while you sleep
- UK Government falls behind schedule to boost 4G signal in rural areas of UK
- Windows 10 users facing new charges from Microsoft get lifeline from Google
- This website wipes all trace of your personal data from the internet
- End of the satellite dish? Sky Q slowly phased out as Sky prioritises streaming
Chester Wisniewski, director, global field CTO at cybersecurity firm Sophos said: “Lockbit rose to be the most prolific ransomware group since Conti departed the scene in mid-2022. The frequency of their attacks, combined with having no limits to what type of infrastructure they cripple has also made them the most destructive in recent years.
“Anything that disrupts their operations and sows distrust amongst their affiliates and suppliers is a huge win for law enforcement.
“We shouldn’t celebrate too soon though. Much of their infrastructure is still online, which likely means it is outside the grasp of the police and the criminals have not been reported to have been apprehended.”
Additional Reporting By Margaret Davis and Martyn Landi, PA Technology Correspondent